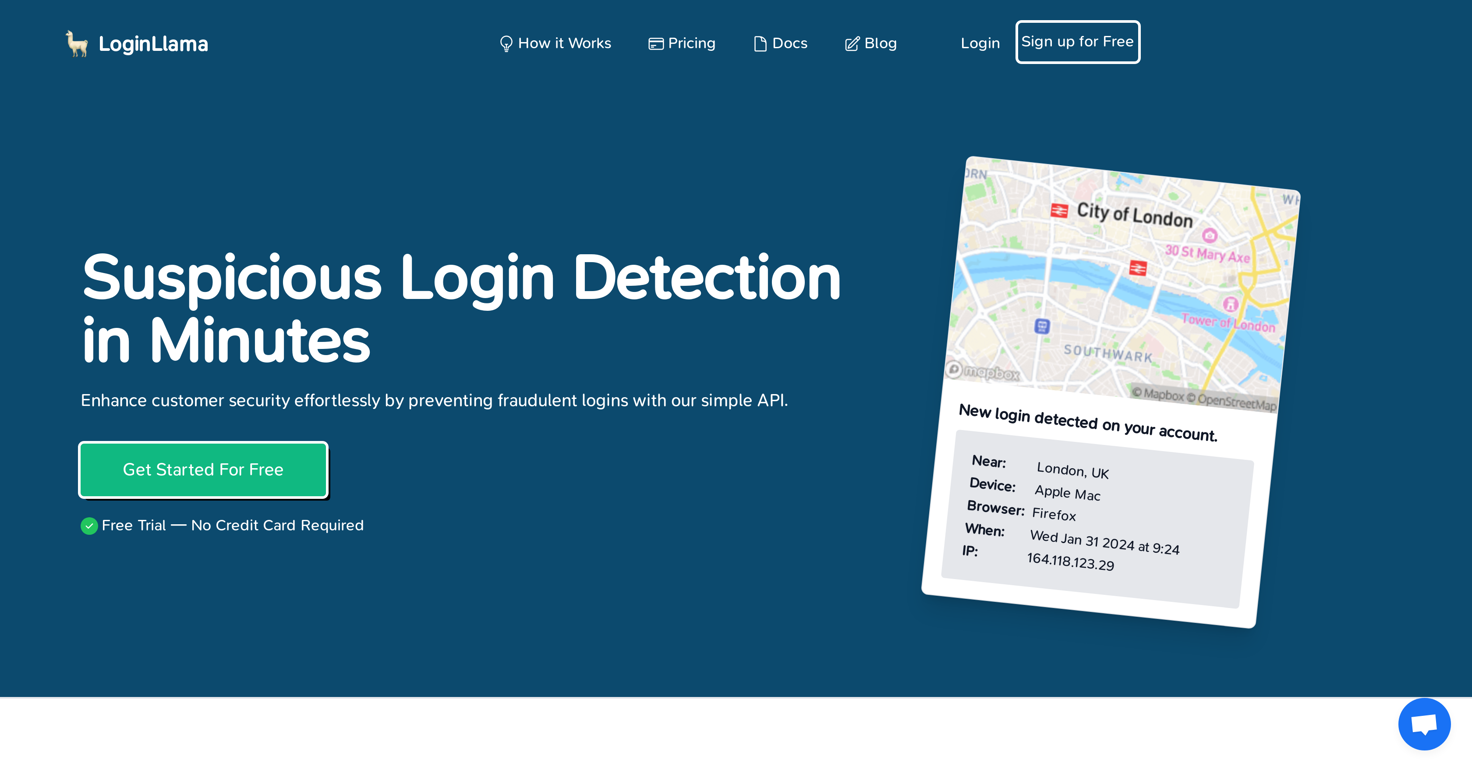
What is LoginLlama?
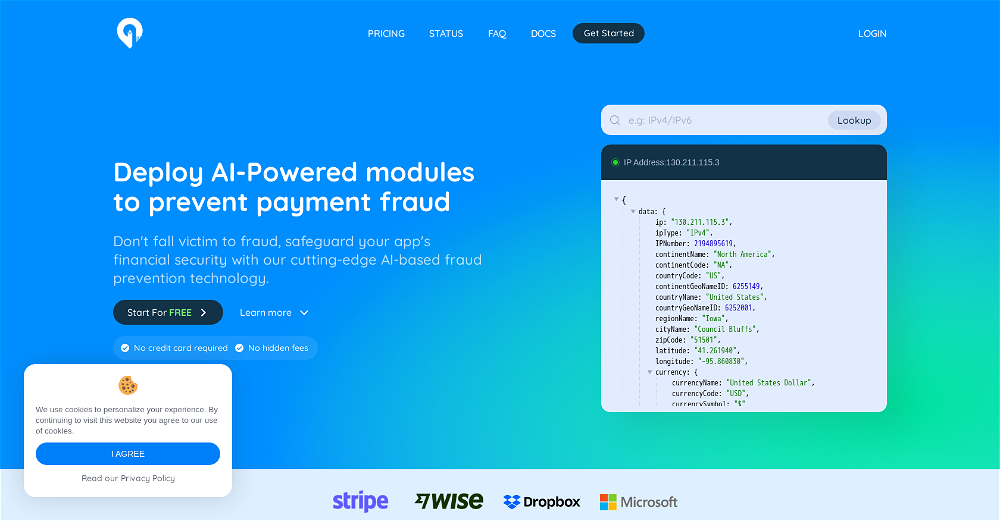
LoginLlama is an API-based cybersecurity tool developed to detect suspicious login activities and prevent fraud for online businesses of every size. By adding an extra layer of security, it offers protection to customers from unauthorized and potential harmful access. The tool is built to handle large-scale traffic and does not require extensive work for setup.
How does LoginLlama detect suspicious login attempts?
LoginLlama uses several ranking factors to decide the potential risk of a login attempt. Employing historic behavior analysis, it observes patterns related to time of the day and location details of login attempts. In addition to this, intelligent AI analysis evaluates login attempts against the user's past behavior. Furthermore, LoginLlama verifies request origins and user agent data for a comprehensive assessment of each login attempt.
What kind of factors does LoginLlama consider when analyzing a login attempt?
Among the factors considered by LoginLlama for analyzing a login attempt include historic behavior patterns of the user especially time of the day and location, AI analysis comparing attempted login to historic behaviour of a user, request origin including IP address and any noteworthy information about it, and user agent details like browser and operating system to validate customer’s usual login patterns.
How does LoginLlama utilize AI analysis to assess login attempts?
AI analysis in LoginLlama acts as an automated judge, comparing the login attempt against the historical behavioural patterns of the user in conjunction with other ranking factors. This AI operates by learning from past data and making informed judgments about whether a login attempt fits the known patterns or deviates significantly, marking it as suspicious.
What are the potential security problems LoginLlama can help solve?
LoginLlama enables resolution for multiple security problems. These include prevention of unauthorized access to sensitive data, detection of potentially compromised accounts, blocking brute force attacks that attempt to gain access using various username and password combinations, identifying and blocking attempts of credential stuffing using stolen data, substantially reducing the effects of phishing and social engineering attacks, and monitoring insider threats by recognizing unusual login activities from authorized users.
How can I integrate LoginLlama into my existing login flow?
LoginLlama can be integrated into your existing login flow in just a few coding lines. Their API is designed with simplicity and ease for quick start-up. An SDK for NodeJS is also in development.
What is the function of sensitivity controls in LoginLlama?
LoginLlama includes sensitivity controls feature that allows granular customization of fraud detection settings according to your unique needs. It provides capacity to set thresholds and rules for triggering alerts easily, letting you take more control over the degree of suspicion that triggers an alert.
What kind of alerts will I receive when LoginLlama detects suspicious activity?
Upon detection of suspicious login activity, LoginLlama provides real-time alerts. These alerts offer an immediate report when advanced algorithms of the tool notice any abnormal login attempt based on their in-depth analysis.
How is LoginLlama scalable to handle large amounts of traffic?
LoginLlama's scalability lies in its API and framework design. Capable of handling large amounts of traffic, LoginLlama's API and infrastructure are built to accommodate the requirements of even the largest enterprises, adjusting to an increase in activity without compromising performance or security controls.
What are the different pricing plans offered by LoginLlama?
LoginLlama offers several pricing plans. The Starter plan is available for $7.99 per month offering 10,000 requests. A Professional plan for $29.99 per month accommodates 50,000 requests. And for an Enterprise plan priced at $99.99 per month, LoginLlama provides unlimited requests. These plans are designed to cater the different needs of businesses.
Is there a free option available for LoginLlama?
Yes, LoginLlama offers a Free Forever Plan. This option allows up to 1,000 requests per month and does not require a credit card for subscription.
How does LoginLlama monitor for insider threats?
For detecting and managing insider threats, LoginLlama monitors unusual login activities by authorized users that may hint at malicious intent or misuse of privileged access. It maintains a careful record of individual user behavior that allows it to recognize deviations that may indicate inappropriate activity.
Can LoginLlama block brute force attacks?
Yes, LoginLlama has the capability to effectively block brute force attacks. By recognizing patterns of repeated attempts to gain access using different username and password combinations, it can reduce the risk of unauthorized access significantly.
In what ways can LoginLlama prevent unauthorized access?
In order to prevent unauthorized access, LoginLlama identifies and blocks suspicious login activities. It adds an extra level of customer security by monitoring usual login patterns, IP addresses, request origins and detected behaviour anomalies to prevent access from unidentified users.
How does LoginLlama help in preventing phishing and social engineering attacks?
LoginLlama aids in preventing phishing and social engineering attacks by identifying and flagging suspicious login attempts which may be originating from these attacks. This reduces the risk and impact of such malicious activities substantially.
In what manner does LoginLlama detect and block credential stuffing attempts?
To prevent credential stuffing, LoginLlama identifies and stops attempts of unauthorized entry using stolen or leaked credentials from other data breaches. By recognizing these patterns, it safeguards user accounts from potential harm.
How does LoginLlama handle user agent data during a login attempt?
During a login attempt, LoginLlama observes the user agent to determine users' browser and operating system. This information is then juxtaposed against where the customer usually logs in, enhancing the overall decision-making process about the nature of login attempt.
How does LoginLlama validate an IP address during a login attempt?
To verify an IP address during a login attempt, LoginLlama checks the IP for information such as its origin, whether it has any history of suspicious activity, or if it is from known VPN providers or a TOR exit node. This enables it to detect potential threats more accurately.
What kind of businesses can effectively use LoginLlama?
Internet businesses of all sizes can effectively use LoginLlama. From small startups to large enterprises, any organization that prioritizes user account security can benefit from this tool by integrating it into their existing login process and thereby secure their customer data.
Is there any forthcoming SDK for integrating LoginLlama?
Yes, a Software Development Kit (SDK) for NodeJS is in the pipeline. This will further ease the process of integrating LoginLlama into existing applications.