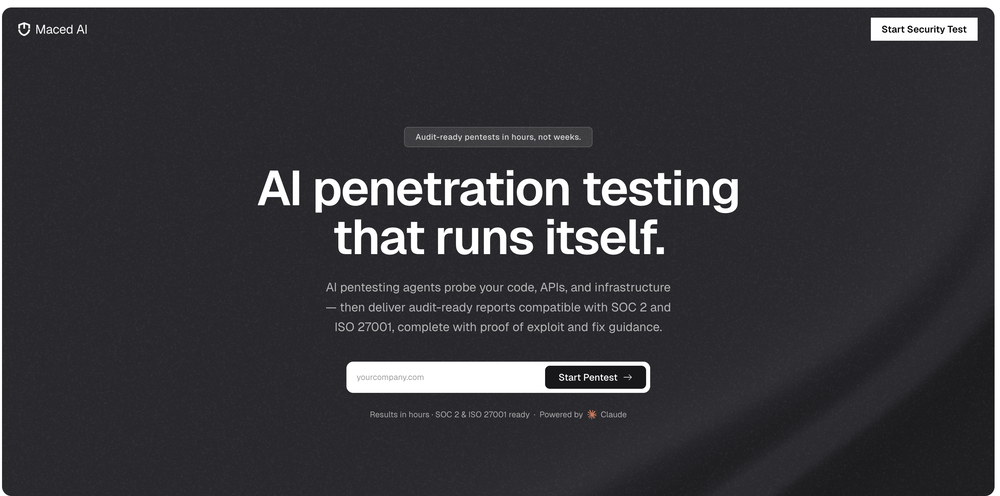
Network security
Featured matches
-
-
-
Open

-

Other tools
- Sponsor
Rocket - Think it. Type it. Launch it.
-
Open
-
Samuel_K🛠️ 1 tool 🙏 3 karmaJan 21, 2026@SocialEchoExcellent platform with AI powered.
-
- Waitlist
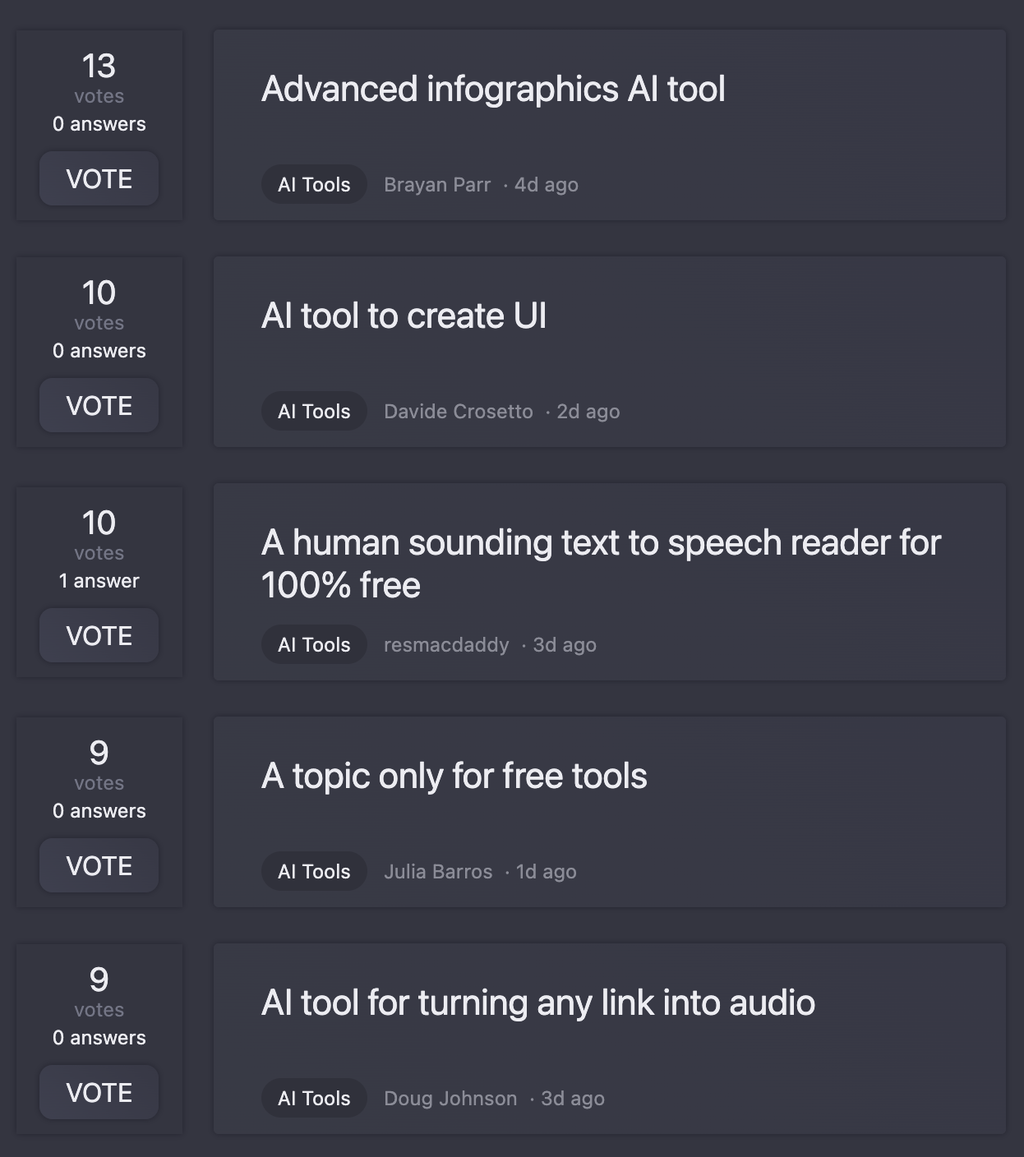
- Didn't find the AI you were looking for?
-
IronClaw feels like how AI agents should’ve been built from the start. Same power as OpenClaw, but your API keys never touch the model.
-
Love that it’s open source. I built a whole GPT content pipeline in a weekend.
-
 OpenGreat tool for quickly assessing any security risks that may be present on a site. Also made a video about it https://www.youtube.com/watch?v=yfHd-vWsUkc
OpenGreat tool for quickly assessing any security risks that may be present on a site. Also made a video about it https://www.youtube.com/watch?v=yfHd-vWsUkc -
ZeroThreat has been a true game-changer for our team. As someone who cares deeply about keeping our retail platform secure, I love how ZeroThreat quietly works behind the scenes, spotting and blocking threats before they become issues—without requiring constant monitoring or technical know-how. The alerts are simple to understand, actionable, and extremely reliable—no more chasing false alarms. Since integrating ZeroThreat, we've seen a noticeable drop in suspicious activity, and I wake up each day knowing our APIs are well-protected. It makes security effortless and gives our whole team peace of mind.
-
seems like a information rake to me every single time i try to make an account it waits til it has all my info then says marked as spam and dont let me in its joke
-
Open
-
 Expert in cybersecurity at KingLand, passionate about cryptography.Open
Expert in cybersecurity at KingLand, passionate about cryptography.Open -
Expert in analyzing vulnerabilities with ransomware focus.Open
-
 Leading global cybersecurity strategies, managing cyber risks, and overseeing information governance.Open
Leading global cybersecurity strategies, managing cyber risks, and overseeing information governance.Open -
 Designing and optimizing seamless network architecture.Open
Designing and optimizing seamless network architecture.Open -
 Ensures efficient and effective network performance and security.Open
Ensures efficient and effective network performance and security.Open -
 Your AI expert in cyber security training.Open
Your AI expert in cyber security training.Open -
 Open
Open -
 Open
Open -
 I'll help you write cybersecurity requirements!Open
I'll help you write cybersecurity requirements!Open -
-
 Advises on wireless communication technologies to enhance organizational efficiency.Open
Advises on wireless communication technologies to enhance organizational efficiency.Open -
 Optimizes cloud-based networks for efficient operations.Open
Optimizes cloud-based networks for efficient operations.Open -
 Expert in CVEs and cybersecurity vulnerabilities, providing precise information.Open
Expert in CVEs and cybersecurity vulnerabilities, providing precise information.Open -
 Assists in identifying and mitigating security threats.Open
Assists in identifying and mitigating security threats.Open -
 Fortifying networks against cyber threats.Open
Fortifying networks against cyber threats.Open